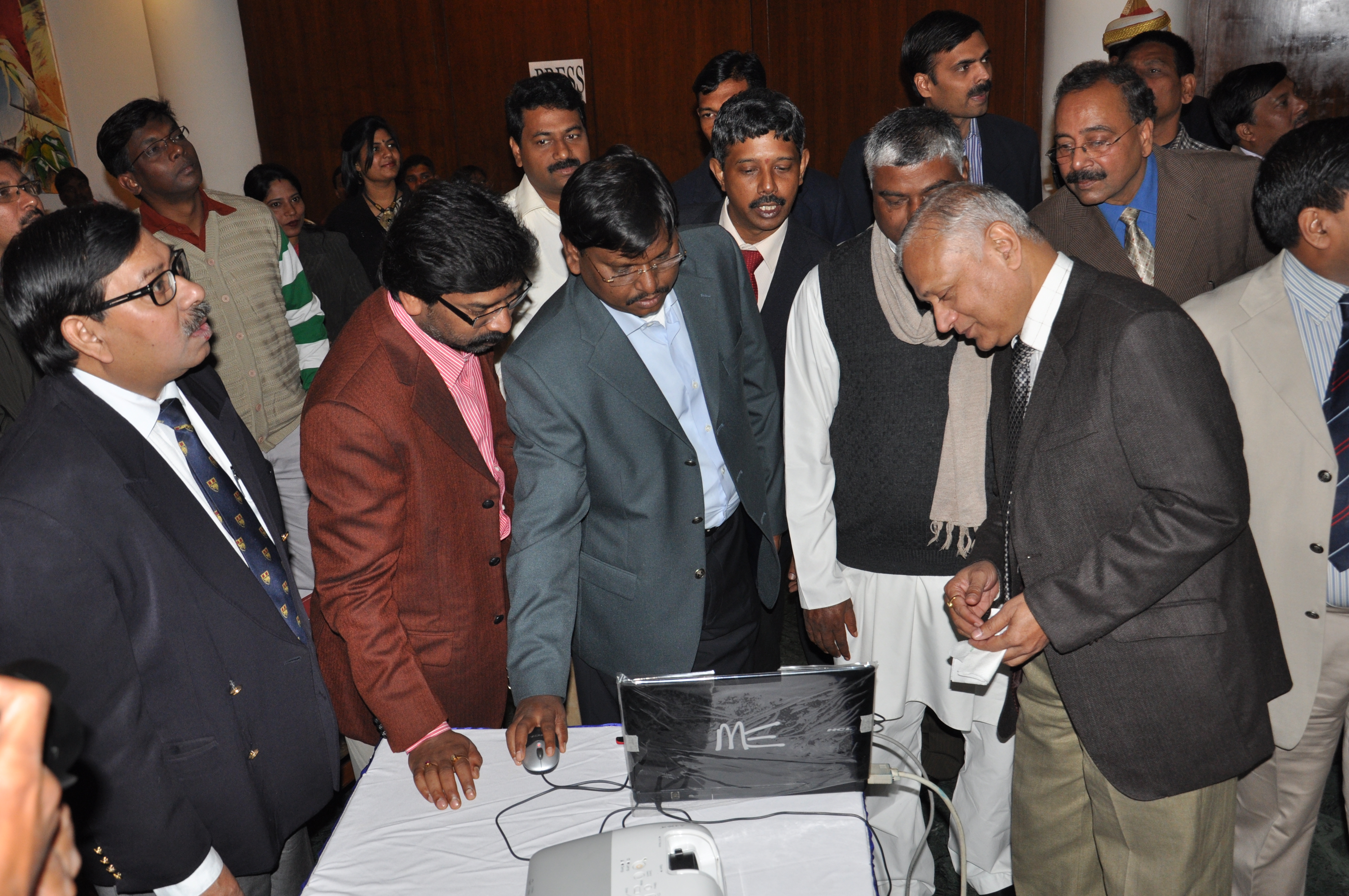
Shri Arjun Munda, Honorable Chief Minister, Jharkhand inaugurated the e-Procurement System of NIC (GePNIC) at Ranchi.
To bring transparency, efficiency, reduce tender cycle time and provide equal opportunity in the procurement process, the Jharkhand government took a landmark decision on 17th December ‘2010 by launching the Government e-Procurement System of NIC (GePNIC) at Ranchi. Speaking on the occasion the Chief Minister, Shri Arjun Munda said in front of the distinguished gathering that his government is committed towards complete transparency in the bidding process and all the departments of the government will join the online system by the end of this financial year. Aware of the major decision and apprehending reluctance in adopting the new system, he categorically stated that departments not adhering to the deadline will be severely dealt with.
Earlier the Chief Minister lighted the traditional lamp and then formally inaugurated the system with the click of the mouse which instantly displayed the site http://jharkhandtenders.gov.in on the two large display screen to the excitement for the gathering which included Cabinet Ministers, Chief Secretary, Development Commissioner, departmental Secretaries, Dr. A. Mohan, DDG NIC, Mrs J R D Kailay, MD NICSI, Mr Shahid Ahmad, SIO, Jharkhand and large number of officials & dignitaries. Deputy CM Shri Hemant Soren also expressed his views and reiterated the decision taken by the government. Shri A K Singh, Chief Secretary expressed similar views and hoped that all the departments will realize the importance of the system and will adopt it as soon as possible. He announced that the government will provide all the necessary support to the departments in this regard. Mr. K.S. Raghvan, STD NIC, Chennai gave a brief presentation about the features and benefits of the system.
The project is a joint effort of NIC / NICSI and initially nine major departments of the government had been selected to adopt the system. Dr. A Mohan said that NIC will provide necessary technical support to make the program successful. Mrs. Kailay told the gathering that taking all the departments at one go is a challenge for which NICSI is fully ready and will provide all the support to make the services successful. The ceremony ended with vote of thanks by Shri N. N. Sinha, Secretary, Road construction who has taken lead in implementing the online system. The presence of other secretaries of the departments showed the importance and priority of the government towards adopting the new system




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


