Book on Empowering India through Geospatial Technologies, Select Stories released by FICCI and Geospatial Today
Anshu Rohatgi, Uttar Pradesh
anshu[dot]rohatgi[at]nic[dot]in
| Feb 6, 2013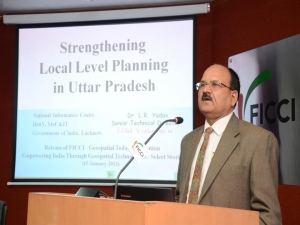

A book titled “Empowering India through Geospatial Technologies – Select Stories” was jointly released by Dr. T Ramasami, Secretary, Department of Science & Technology and Dr. Shailesh Nayak, Secretary, Ministry of Earth Sciences, Government of India on 15th January 2013 in the FICCI Auditorium, New Delhi.
Three case studies oral presentations were also conducted during the book release function. “Strengthening Local Level Planning in Uttar Pradesh” was presented by Dr. L. R. Yadav, Senior Technical Director, NIC, UP State Unit, Lucknow.
News Submitted by Dr. L.R. Yadav, STD, NIC, Uttar Pradesh.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


