Governance
Ease of Doing Business in Assam - Making life easier for the citizen
The EODB platform (https:// eodb.assam.gov.in) was developed using the Open, Secure and Scalable Framework ServicePlus, to facilitate for filing, management, and tracking of all necessary clearances, approvals, registrations, and renewals under various State enactments. The Single Window...
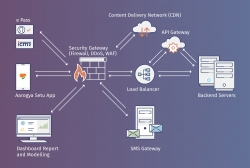
Aarogya Setu App
Aarogya Setu is a mobile application launched by the Government of India on 2nd April 2020, to aid the COVID-19 containment efforts of the Government. The App works based on contact tracing method and helps in identifying, monitoring and mitigating the spread of COVID-19 across the country
Lifeline UDAN Portal - Ensuring steady supply of essentials through airways
All domestic and international flight operations were suspended by the union government with the implementation of lockdown on 25th March 2020 to contain the spread of Coronavirus in the country. However, the transportation of medical supplies and essentials goods needs to be ensured to even a...
RT-PCR App - Mobile Application for Containment and Monitoring Covid-19 pandemic across the Country.
Covid-19 pandemic in India is part of the worldwide situation of coronavirus disease and a large number of people is likely to be affected by the coronavirus. The country has imposed initial lock-downs, supplemented by increased testing of people and contact tracing of patients as effective measures...
Gujarat CM Dashboard - Enabling government machinery for strengthening good governance
The system first of its kind was an innovation in terms of accessing data from all e-Governance applications of the State of Gujarat and providing the same for monitoring against defined KPIs. In the reverse, CMO could drill down to the granular level on the fly for red-flagged items and intervene...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


