Trainings
eFMAS Training conducted in Chhattisgarh
National Rural Livelihoods Mission (NRLM), Ministry of Rural Development, Government of India, in technical coordination with NIC – RD has developed a software module namely Electronic Fund Management cum Accounting Solution (eFMAS), as part of NRLM eGov application (https://nrlm.gov.in), to...
Symposium on Data Analytics on 1 Dec 2021 at Assam Administrative Staff College in collaboration with NIC Assam
A one day symposium on “Data Analytics” was held at the Assam Administrative Staff College, Government of Assam. The event was held in collaboration with the Centre of E-Governance, Assam Administrative Staff College, Guwahati and National Informatics Centre, Assam and Centre of Excellence...
Symposium on Artificial Intelligence (AI) and Internet Of Things (IOT) at Assam Administrative Staff College (AASC) on 2nd November 2021
A one-day Symposium on Artificial Intelligence (AI) and Internet of Things (IOT) was held by the Centre of e-Governance, at the Assam Administrative Staff College, Government of Assam in Collaboration with National Informatics Centre, Assam. The Symposium was attended by Officers of the Government...
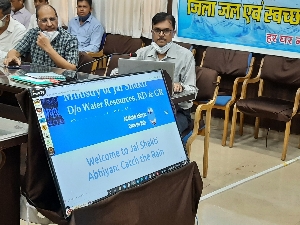
Capacity Building on Jal Shakti Abhiyaan "Catch the Rain, Where it Falls, When it Falls" (JSA: CTR) Portal at Dhamtari, District, Chhattisgarh
JSA:CTR campaign was launched by Hon’ble Prime Minister on 22nd March, 2021. As per the instructions of Jal Shakti Mantralay, GoI, every district must prepare inventory of existing water bodies within district using the JSA portal. For the smooth implementation of Jal Shakti Abhiyaan,...
Workshop on CPGRAMS and RTPS for all the Public Grievance Officers of the Service Delivery Departments
Administrative Reforms, Training, Pension & Public Grievances Department, Government of Assam and ARIAS Society in collaboration with NIC, Assam State Centre, has organized a Workshop on RTPS and CPGRAMS for all the Public Grievance Officers of Government of Assam on 13th September...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


