Cyber Governance
e-NIYANTRAN : Online Time Card System to save the migrating wildlife of Kaziranga National Park, Assam.
e-Niyantran will replace the existing Manual Time Card System of regulating the vehicular movement on NH-37, the highway which runs parallel to the southern boundary of Kaziranga National Park. The system would help avoid accidental death of wild animals while they cross the highway, especially during...
PEHCHAN - Simplifying the Civil Registration in Rajasthan Digitally.
Since its inception in 2014, over 1.28 Crore registrations have been done through Pehchan. Citizens are facilitated for applying online and receive digitally signed Registration Certificate by email, and downloadable from the portal. About 12,500 Registrars & Sub Registrars and 1,000 private hospitals...
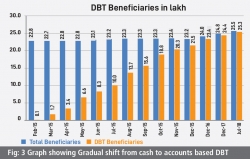
JOURNEY OF DIRECT BENEFITS TRANSFER (DBT) IN HARYANA (1966-2018) : Strengthening and enhancing DBT service in the interest of beneficiaries.
The State Government, in 2014 decided to disburse social security pension benefits directly to the accounts of beneficiaries using the concept of Direct Benefit Transfer. More than 62 Scheduled Banks, their BCAs, Post Offices etc. were engaged for opening, uploading, updating & crediting the beneficiaries...
e-ABGARI - Complete IT Driven Supply Chain Management System for State Excise.
The project is built on the methodology of Reduced discretion - Electronic workflow - Electronic service delivery, adopting a web-enabled delivery mechanism to ensure the delivery of G2B, G2C, G2G services in a timely, transparent, more accessible and reliable manner.
VIVID - weaving a Digital India
VIVID'18, the 2nd season of the National Meet on Grassroot Informatics organized by NIC was held in New Delhi at India Habitat Centre during 8th to 10th February 2018. An extensive platform to 240 NIC District Officials from across the country to share their knowledge, interact & leverage each...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


