Cyber Governance
DevSecOps - Producing high quality, secure software at pace
Enterprises across the world are demanding software release at high speed to meet business requirements. when software is developed at such speed, security should not be left behind which can only happen if security is built in to SDLC. Such requirements gave birth to technologies like Agile...
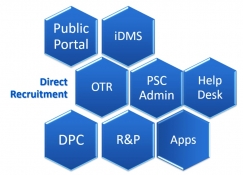
PSC-Soft Public Service Commission Software for Transformation
The PSC-Soft provides an integrated solution for the core functions of any State Public Service Commission with focus on providing user friendly interface for applicants with one-time registration facility. It is highlighted by the fact that during initial implementation stage in HPPSC, the...
eCabinet - Automate Cabinet meetings in paper free and virtual mode
eCabinet/ eMantrimandal is a powerful software portal for State governments to conduct Cabinet meetings electronically and online mode. Developed by NIC, it maximizes usage of technology in meetings and reduces paper use. eCabinet automates work flow activities of meetings; before, during and after....
Ajmer District, Rajasthan Ambitious and determined, set on a digital journey for better e-Governance
Being the Division HQ of Rajasthan and located in the centre of the State, Ajmer District is home to many important offices such as Rajasthan Board of Secondary Education and Revenue Board Rajasthan. The District also has various pilot runs like the famous Rural Connectivity Project demonstrated...
Suraksha Suite of Arunachal - Enabling Arunachal Pradesh Police to spot and reach out to distressed citizens & tourists
Ensuring safety of its citizens is one of the prime responsibilities of any government. The Arunachal Pradesh State Police is the arm of the government to take timely measures to ensure adequacy of security and safety of the public. It is with such an intent, the Arunachal Pradesh Police has entrusted...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


