e-Services
Goa: Making a Difference through e-Governance
The coastal state of Goa known for its swaying palms, sunny beaches and progressive life style has not been far behind in the field of information technology. Having bagged the prestigious CSINIHILENT: Most Progressive e-Governed State Award in 2006-07 the last few years have seen Goa leapfrog...
Smart Card Based Projects in Government
Computer chip-embedded plastic cards that store and transact data, Smart cards, a new form of fast and effective transaction has been instrumental in providing better egovernance in India. Smart cards usually have multipurpose lives, from being National ID cards to tools for driving licenses...
Karnataka: Empowering Rural Citizens by Taking ICT to Their Doorsteps
Bridging the gap between the haves and the havenots has been the focus of the Government of Karnataka. The aspiration is being fulfilled by continuously providing more and better services to the citizens. The rural citizens are empowered by taking ICT to their doorsteps thus enabling them...
Tripura: Focusing on IT Enabled Services
Tripura, a landlocked hilly state, bounded on the north, west, south and south-east by Bangladesh and in the east with Assam and Mizoram, has a tropical climate and the main languages spoken are Bengali and kokborok. Rice is the principal crop followed by oilseed, pulses, potato and sugarcane....
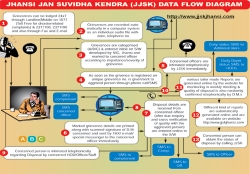
Jhansi: Leading From the Front
'Leading from the front' is synonymous with Jhansi, be it the First Freedom Struggle of India or the modern day ICT based Governance, Jhansi has been the torch bearer with earnest dedication. Centuries have moved from twentieth to twenty first but the will to provide good governance...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


