e-Services
eNirvachan : An online Polling Personnel Management System for Election Department of Assam
e-Nirvachan (Assam) is a solution product developed by NIC Assam for the management of election processes. It can be used for any election, be it parliamentary or assembly or any state level (Panchayat/Council) election. Initially, in order to ease the processes of manpower management for an election,...
Public Financial Management System : Facilitating digital inclusion and accelerating transformation to a Digital Economy
The Ministry of Finance has taken a big leap forward, with PFMS emerging as one of the largest financial management systems in the world, critical in bringing about transformational accountability and transparency in financial management and promoting good governance.
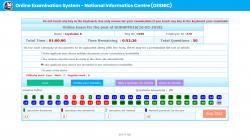
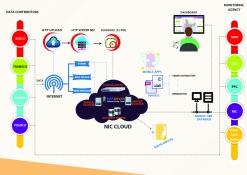
Online Examination System of NIC (OESNIC) : Boasting of a robust architecture enabling the simultaneous operation of multiple exams
OESNIC has replaced the existing examinations, conducted using paper, with online paperless system in government departments and schools, thereby ensuring 100% transparency in conducting examinations and mark sheet evaluation. Till date, more than 60 examinations have been conducted for NIC...
National Power Portal : Providing comprehensive framework for Power Sector data capture and dissemination
National Power Portal (NPP) is a unified system developed for Indian Power Sector to facilitate online data capture/ input (daily, monthly, annually) from generation, transmission and distribution utilities in the country and disseminate the power sector information (operational, capacity, demand,...
Anubhav Portal : A platform for retirees to cherish work life moments and help channelise enhancement in internal processes
Operated by the Department of Pension & Pensioners' Welfare under the Ministry of Personnel, Public Grievances & Pensions, Anubhav is the dream project of the Honorable Prime Minister. It provides a platform to retiring employees to share their experiences of working with the government...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


