Digitization
Department of Justice
Department of Justice is a part of Ministry of Law & Justice and is one of the oldest Departments of Govt. of India. The functions of the Department of Justice include the appointment, resignation and removal of the Chief Justice of India, Judges of the Supreme Court of India, Chief Justices and...
National Voter Services portal
National voter’s services portal is owned by the election commission of India which is a permanent Constitutional Body. The Constitution of India has vested in the Election Commission of India the superintendence, direction and control of the entire process for conduct of elections to Parliament...
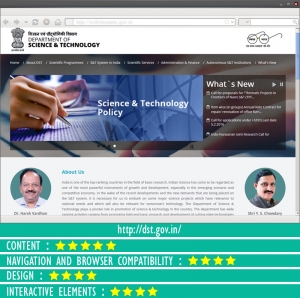
Department of Science and Technology
The Department of Science & Technology plays a pivotal role in promotion of science & technology in the country. The department has wide ranging activities from promoting high end basic research and development of cutting edge technologies on one hand to provide service to the technological...
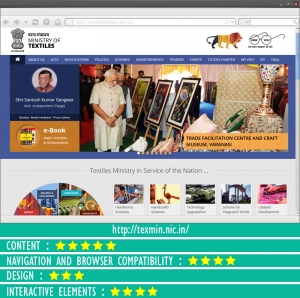
Ministry of Textiles
The indigenously designed website of ministry of textiles is endowed with up-to-date content arranged in two broad categories on the Homepage which showcases the different sectors and schemes of the Ministry. The website makes rich use of colors and graphics to highlight the different sections. It...
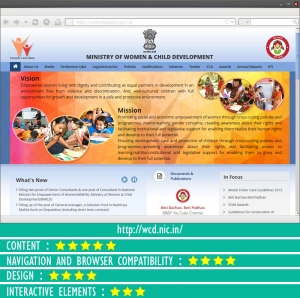
Ministry of Women and Child Development
The Department of Women and Child Development, Government of India, came into existence as a separate Ministry with effect from 30th January, 2006; earlier since 1985 it was a Department under the Ministry of Human Resources Development. The Ministry was constituted with the prime intention...




 Subscribe
Subscribe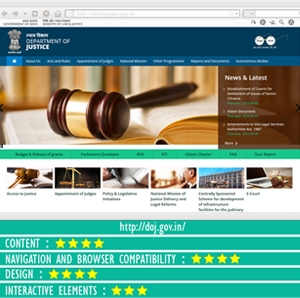


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


