Digitization
e-Archives: Online Cataloguing System for Odisha State Archives, Bhubaneswar
e-Archives is an online cataloguing system developed by NIC for Odisha State Archives(OSA) to facilitate systematic collection (scanning and storing), preservation, management, publication and educational use of the rare records and historic documents digitally. One of its kinds, the e-Archives software...
e-Services for Council of Higher Secondary Education - A successful approach in Manipur
NIC Manipur has been providing ICT services to the Council of Higher Secondary Education, Manipur (COHSEM) since the year 2003. In the year 2004, the Application software for omputerization of the entire process of examinations conducted under this council was developed and the results of these examinations...
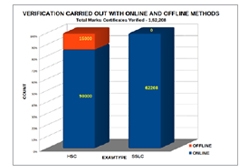
Mark Certificate Verification System for Directorate of Government Examinations, Tamil Nadu
The Directorate of Government Examinations conducts massive board examinations, for which they issue about Eight lakhs of Higher Secondary Course Certificates, Twelve lakhs of Secondary School Leaving Certificates and Fifty thousand Diplomas for Elementary Education every year. The National Informatics...
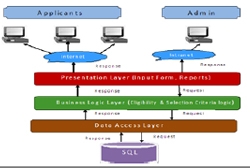
Online Internship Management System for NITI Aayog
National Informatics Centre (NIC) unit at NITI Aayog has been actively involved in development and implementation of various e-Governance applications. Internship Management System is one such initiative to facilitate engagement of Indian Nationals as Interns in NITI Aayog. The system ensures a convenient...
Village level online e-Services in Goa: Taking Governance to the grassroots
The beautiful State of Goa is geographically small compared to many other Indian States. The long Konkan terrain spreading across its many regions and the limited availability of public transportation system makes the travel especially for those from the farflung villages quite difficult. Citizens had...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


