G2C
Oral Pre-Cancer Mobile App
The innovative App is very useful for Doctors and Dental Assistants in the diagnosis process and management of oral cancer in its early stages. ICT thus helps improve the quality of life of the citizens and saving lives using the best that ICT has to offer.
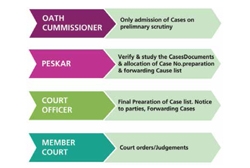
Revenue Court- Case Monitoring System of Odisha
Petitioners can now register a case online and track its status. Cause list is generated dynamically, which is published on the portal after approval by the competent authority. Hearing Notice is served online to the petitioner/ advocate and opponents by way of SMS, e-mail and physically through the...
District Bhojpur, Bihar
District Bhojpur has been striding ahead in a progressive path of e-Governance since 1988 with the establishment of NIC Unit in the district. NIC continues to be instrumental in successfully implementing several ICT based initiatives. The achievements story continues.
District Namchi, Sikkim
NIC South District Unit of Namchi was established in the year 1993 and since then had a key role in promoting e-Governance in the District using Information and Communication Technology. Many software applications, websites and mobile apps have been developed and implemented with an objective to bring...
District Chamba, Himachal Pradesh
The IT revolution in Chamba kick started with the establishment of NIC District Centre in the year 1988 aiming at providing IT Support and Services to various Government and Public sector Departments. Since then, ICT has played a pivotal role in improving e-Governance and delivery of citizen centric...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


