G2C
East Godavari, Andhra Pradesh
East Godavari NIC Centre provides ICT based solutions to the District Administration and various Central, State and Quasi Government offices located in the district. It is the first district in the Country to utilize Aadhaar based biometric authentication services for Government To Citzens (G2C) Applications.
DND Services App of TRAI
Subscribers can activate the Do Not Disturb (DND) Services by TRAI by using this App. By activating the DND services, the telecom provider can block/ take action against the numbers from which consumers are getting such calls or messages.
ServicePlus
A versatile application that allows Government officials and departments to quickly and easily create, format, publish forms, notifications etc., ServicePlus has a simple drag and drop functionality, in addition to many other advanced features, which makes it unique.
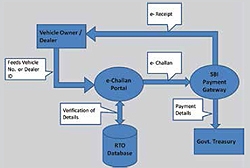
ePayment Services in Goa
With the Government of India taking steps to promote online and digital payments, the migration of the services to the ePayment channel represents major strides towards achieving decreased dependence on cash. The initiative by Transport Department, Government of Goa to allow citizens to pay the various...
National Register of Citizens in Assam
The National Register of Citizens in the State of Assam has been one of its kind exercise in the country and aims to touch the lives of all the citizens in Assam. The task had long been deemed impossible, but the National Informatics Centre (NIC) has risen to the challenge and done commendable work




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


