Articles
Raigarh: Extending IT to Masses
The cultural capital of Chhattisgarh, having a glorious historical background, Raigarh is the land of a music legend 'Kin Chakradhar Singh' who was a maestro of Tabla and Kathak and is the founder of famous Raigarh Gharana of Kathak. The district is rich in minerals like coal, quartz and dolomite....
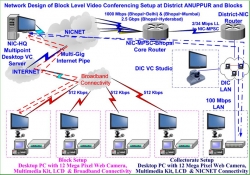
Anuppur: Serving Administration and People with ICT
Situated in the north eastern part of Madhya Pradesh, Anuppur shares its geographical boundaries with Shahdol and Dindori districts of Madhya Pradesh and Bilaspur and Koria districts of Chattisgarh.The district was formed in the year 2003 and is popular among tourist for 'Amarkantak', the originating...
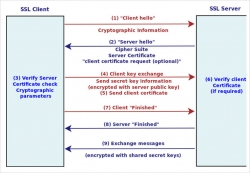
Secure Your Server Through SSL
In the recent times, we have been using the Internet for many of our online transactions such as Online Ticket reservation, online banking etc.We also observe that at times the data / information are being hacked without the knowledge of the user. However, technology can be used to minimize the risk...
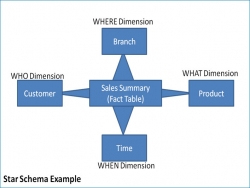
Multidimensional Data Modelling Concepts
Multidimensional data modelling is used for the designing Data warehouse, which will help in surround facts with as much relevant context dimensions. Multidimensionality is a design technique that separates the relational data into facts and dimensions. Multidimensional model present information to the...
Contribution of NIC to Government of Bihar in the field of ICT
National Informatics Centre has its wide presence in Bihar besides the 38 districts of the State.These centres have been instrumental in accelerating the pace of e-Governance with ICT-led initiatives and developments using the infrastructure of NIC e.g. NICNET, Data Centre, Video-Conferencing, etc. Regular...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


