Workshop for Capacity Building Program on IVFRT Organized at Muzaffarpur in Bihar
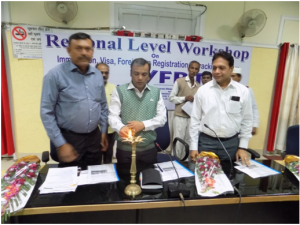

2nd Regional Districts Workshop at Muzaffarpur was inaugurated on 1st March 2016. Sh. Dharmendra Singh, District Magistrate, Muzaffarpur and Sh. Rajesh Kumar Singh, State Informatics Officer inaugurated the workshop in presence of participant from FRO and NIC.
District Magistrate addressed the participants and stressed on the importance of capturing online data under the envisaged IVFRT system to facilitate legitimate travellers and enhance security measures.
Sh. Rajesh Kumar Singh, State Informatics Officer stressed on the importance of sharing of information among stakeholders and informed the participants for up-coming various project of Ministry of Home Affairs for better integration and information sharing.
Sh. S K Shrivastava, Technical Director also addressed the participants. Sh. Rajiv Ranjan, IVFRT Coordinator, in his technical session discussed, interacted and addressed the participants from FRO side of Tirhut and Darbhanga Zone along with participating District Informatics Officers and representative of Hotels. There were discussions on issues and processes to deliver services.
Earlier, Sh. Navin Suman, DIO, Muzaffarpur welcome the participants. Sh. Praveen Jha, ADIO Muzaffarpur provided necessary coordination and ICT facility for the workshop.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


