Nagaland: Jeevan Pramaan Camp for ex-servicemen held at Wokha on 2nd & 3rd July 2015

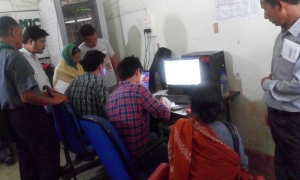
Jeevan Pramaan Camp for the ex-servicemen of Wokha District was held on the 2nd & 3rd July, 2015 at NIC Wokha District Centre, DC Office Complex, Wokha, Nagaland.
The camp co-incided with the Digital India Week celebrations at Wokha District, wherein a total of 144 pensioners were issued the Digital Life Certificates.
The event was organised by Rajya Sainik Board, Nagaland, Kohima led by its Director, Brig. K. K. Roy Choudhary, SM, VSM (Retd.).
Shri. George Kath Rengma, DIO NIC, Wokha District Centre and his team provided active technical support throughout the camp days.
NIC Co-ordinator for Jeevan Pramaan in Nagaland, Shri. Lanusungkum Aier, PSA and team member, Ms. Novotsono Natso, Sc. Officer, were present at Wokha on the first day of the camp to provide necessary technical support and setting up the systems for the successful conduct of the camp.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


