INTRA-IPS Portal Launched
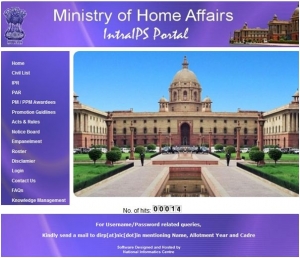
INTRA-IPS (http://intraips.gov.in) official website has been launched by Shri S. Jayaraman, Special Secretary-Internal Security, Ministry of Home Affairs, at New Delhi on 8th April 2013. This exclusive website for Indian Police Service (IPS) officers will help them to access all matters concerning their 'service' from anywhere in the country. The website has been designed, developed and hosted by National Informatics Centre, North Block, MHA, New Delhi under the leadership of Ms. Suganthi M. P, Technical Director, NIC and Shri S. Chandran, NIC, Technical Director and overall guidance of Dr. B. N. Shetty, DDG, NIC. The salient features of this website are availability of Indian Police Service Civil List, Immovable Property Returns, Latest Notifications/ Circulars, Rules, Police Medal Awardees list etc. related to all IPS officers all over India.
Furthermore, important decision is also taken that all Indian Police Service (IPS) officers will be issued new e-mail addresses by MHA. The Knowledge Management System (KMS) will be made part of this Portal wherein IPS officers will be able to upload and share knowledge resources which will be useful to IPS community. The efforts of NIC for the timely launch of above website were highly appreciated by all.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


