Launch of State Portal, SSDG & eForms in Uttar Pradesh
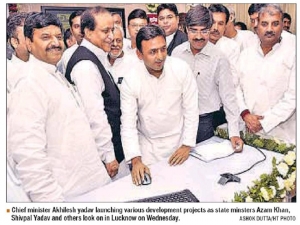
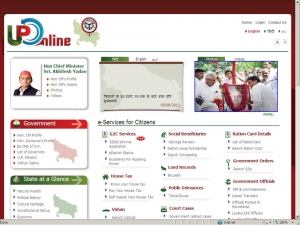
Hon’ble Chief Minister of Uttar Pradesh Sri Akhilesh Yadav launched the State Portal and eForms on 1st August 2012. The State Portal (uponline.up.nic.in) and eForms are developed by NIC UP State Unit. With the launch of eForms, Citizen is now able to get the 26 services of the 8 departments from their nearby CSC/Lokvani Centres. On this occasion Hon’ble Chief Minister praised the efforts being made by NIC Uttar Pradesh and State IT deprtmant .
The Senior Cabinet Ministers of Government of Uttar Pradesh Sri Azam Khan, Sri Shivpal Singh Yadav, Sri Ambika Chowdhary , Sri Ahmed hasan and Sri Abhishek Mishra were graced the occasion. Various Senior Administrative Officers of Govt. of UP were present during the launch. The Commissioners and District Magistrates also inaugurated the services from CSC Centres in their respective Commissionery and District.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


