Launching of Online Inventory Management System for NIC Nagaland
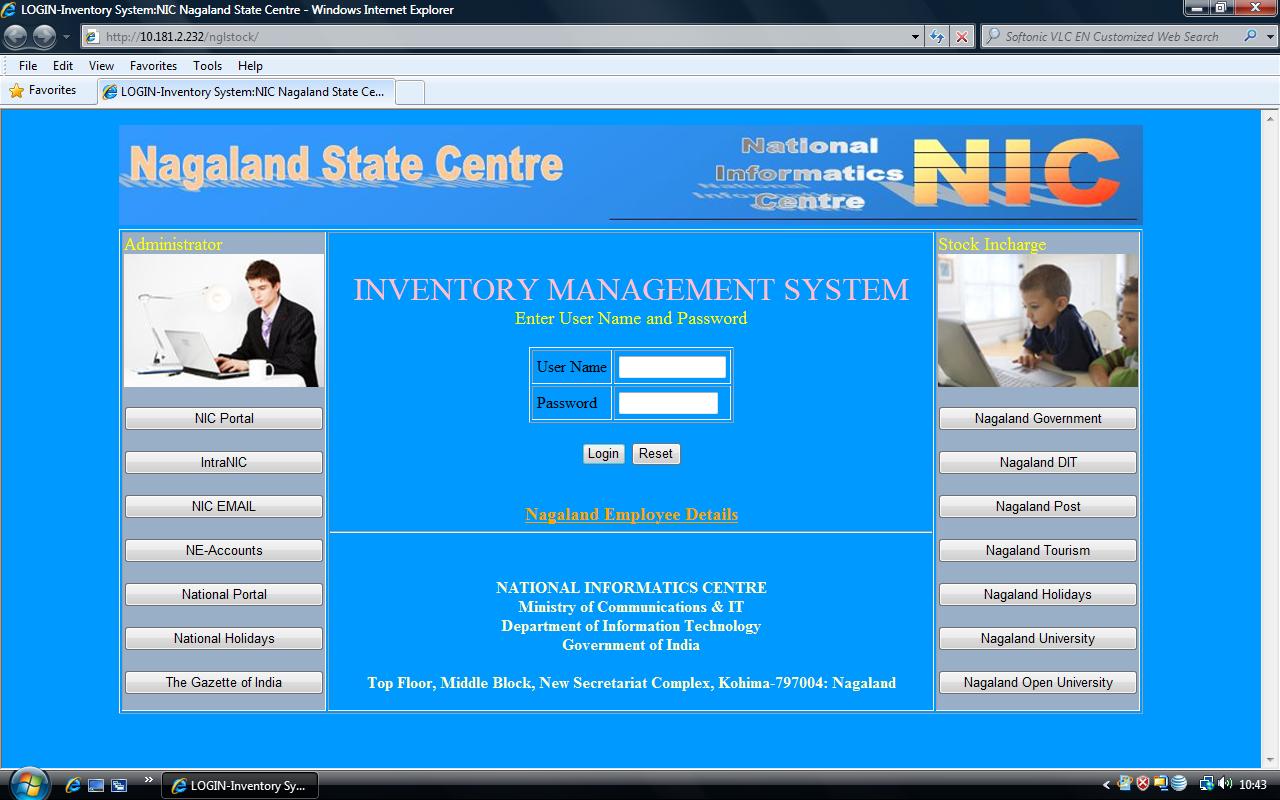
The in-house application for Online Inventory Management System developed by NIC Nagaland State Centre for NIC internal use was formally launched by Mr. Kezungulo Medikhru, SIO on 15 November 2010 in the presence of Shri. Vinay Thakur, STD & NE States Coordinator, NIC Hqr. New Delhi and the DIOs through Video Conference.
The online application aims at meeting the urgent and actual information requirement of NIC hardware items at any point of time. It will also help the users to keep track of the records and understand the inventory status. The web application contains several web pages designed by using ASP with Oracle 10g R2 as RDBMS. The Application is mounted on Window Server 2003 platform with Internet Information Server as Web Server in NIC Data Centre, Kohima.
The main feature of the online application are as follows:
i) To keep record of all hardware item-wise as per the Purchase Order No. at State Centre or District Centre.
ii) View item details in the Stock- district-wise.
iii) To enable the users to look for information details of hardware items in various NIC Centres in the State.
iv) Placement of items with installation details and against whom the items have been issued.
v) Generate report based on Purchase Order No. & Date, Location, Item Name, Installation Date, etc.
The site is available for authourised users at http://10.181.2.232/nglstock




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


