Sh. Gurudas Kamat, Hon ble Min. of State for Home Affairs and Comm. and IT, Govt. of India launched Mobile Money Transfer Service on through NIC s VC
Sarbjeet Singh, Punjab
singh[dot]sarbjeet[at]nic[dot]in
| Jun 3, 2011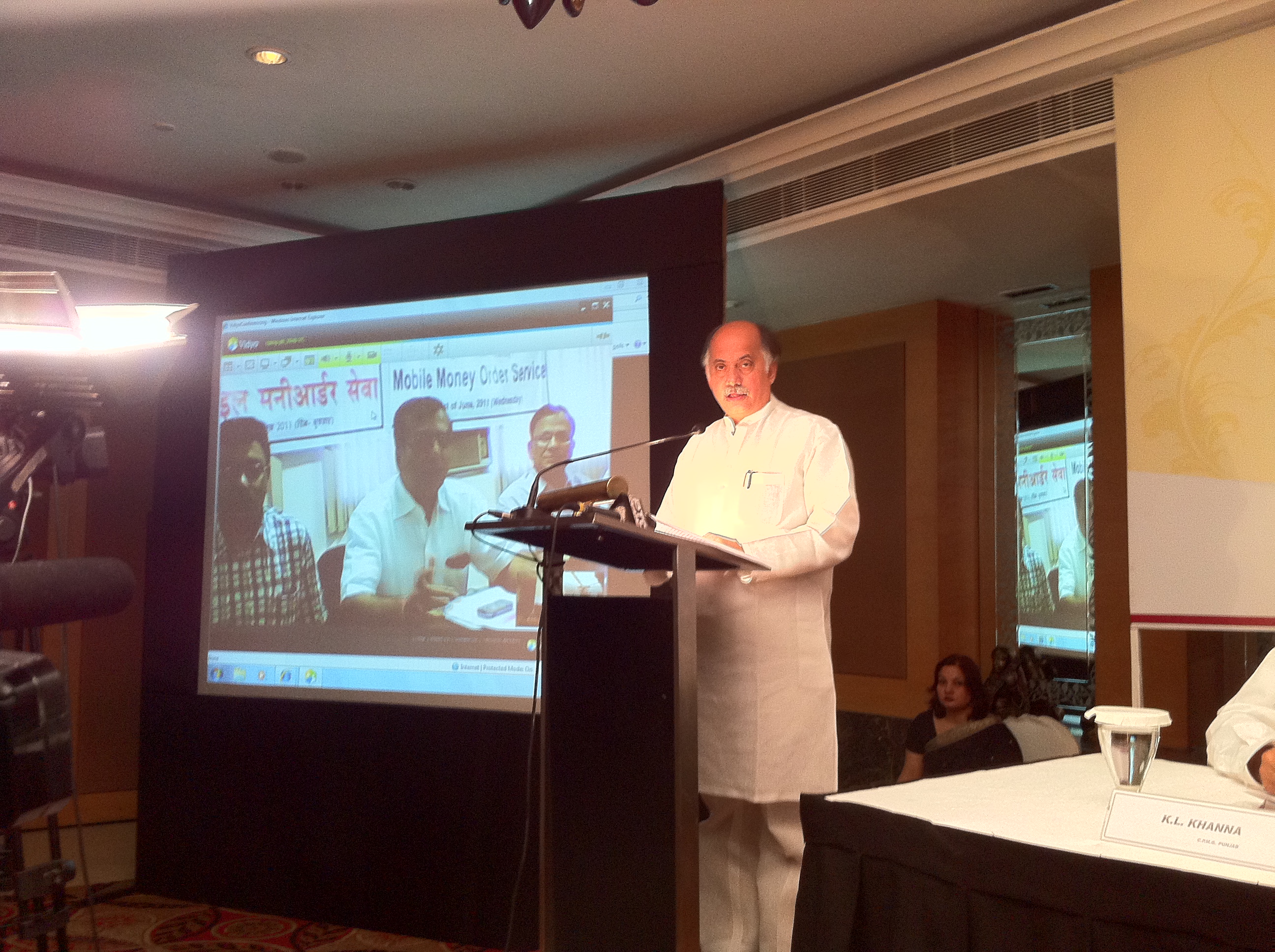
Sh. Gurudas Kamat Hon ble Minister of State for Home, Communication andIT launched Mobile Money Transfer Service of Department of Post at




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


