Chief Secretary, Punjab inaugurates VAHAN software at District Fatehgarh Sahib
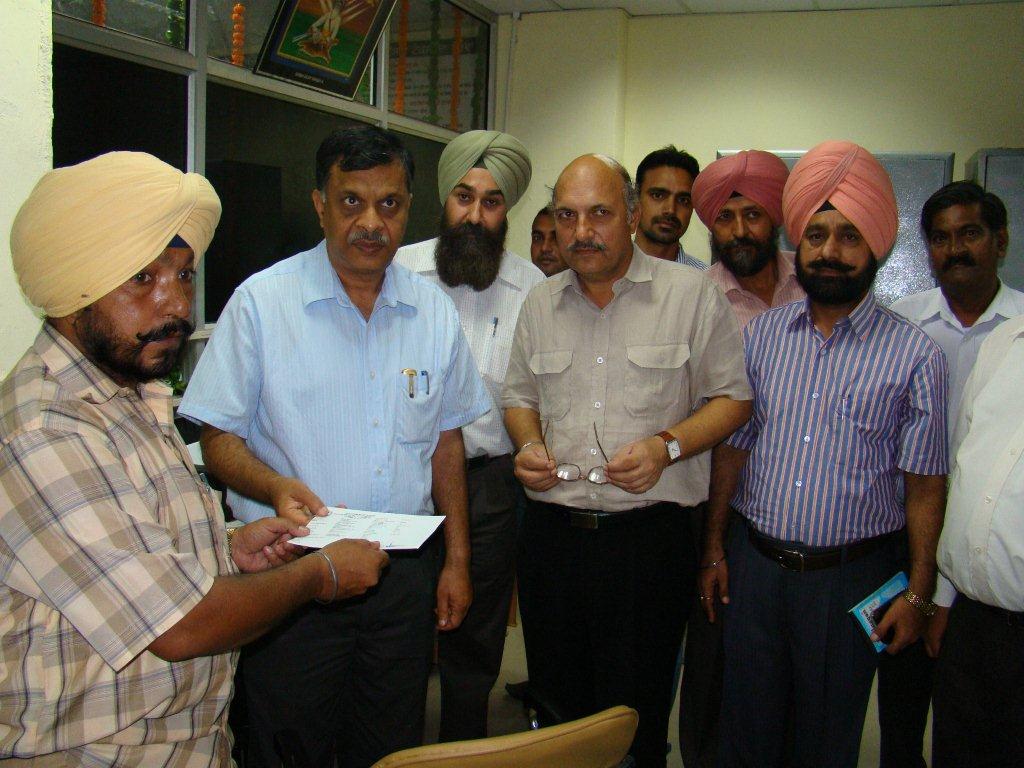
Chief Secretary, Punjab Sh. S.C.Aggarwal launched the VAHAN project on 06-08-2010 at district Fatehgarh Sahib of Punjab state. He handed over the first Vehicle Registeration Certificate to the owner of vehicle. Appreciating the efforts of National Informatics Center in implementing VAHAN Project in the district, Sh. S.C. Aggarwal said that with the implementation of VAHAN, district will be hooked to State as well as National database of Vehicles and the details of owner of a vehicle would be available on click of mouse. He said that by computerizing Transport department, the district has moved one step further towards e-Governance.
He further emphasized on the need for the computerization of other activities of the District Transport Office like issuance of driving license and enforcement. DC, Fatehgarh Sahib, assured that administration would soon get SARATHI implemented in the district. DIO, Fatehgarh Sahib provided a brief overview of VAHAN software and benefits that would be derived by the computerization of Vehicle Registration.
Senior officers from NIC-Punjab and Transport department were also present on the occasion. Chief Secretary also had detail discussions and demonstration of other NIC projects implemented in Fatehgarh Sahib such as SUWIDHA, Property Registration System etc.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


