J&K Finance Minister Jenab A.R. Rather launches Funds organization Website
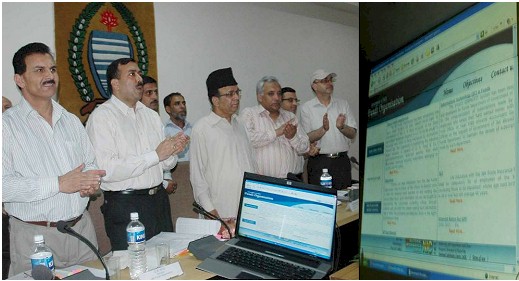
JAMMU, APRIL 28- Hon’ble Minister for Finance and Ladakh Affairs, Jenab Abdul Rahim Rather, today launched the official website of J&K Funds Organization, in a very simple but impressive function. The website was developed by NIC J&K and hosted at http://jkfunds.nic.in. Speaking on the occasion, the Minister said that the purpose behind computerization of Accounts and launching of its website was to update of General Provident Fund (GPF) accounts for the convenience of subscribers and providing them GPF data on internet in a password protected manner.
Commissioner/Secretary, Finance Mr. Sudhanshu Panday, Director General, Accounts and Treasuries, Mr. Wali Muhammad Bhat, Director Audit and Inspection Mr. M. I. Khanday, representative of J&K Accountant Generals Office and other concerned senior officer of Finance were present on the occassion. NIC J&K team was represented by Shri Abhay Kumar, TD and State Informatics Officer, Shri Suresh Kumar, Scientist ‘D’, Sh Raman Gupta, Scientist ‘B’ and Sh Baiju Ubbott, Scientist ‘B’.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


