Commissoner/Secretary, P&DD reviewed progress of development schemes thru VC
Jit Raj, Jammu and Kashmir
jit[dot]raj[at]nic[dot]in
| Oct 26, 2009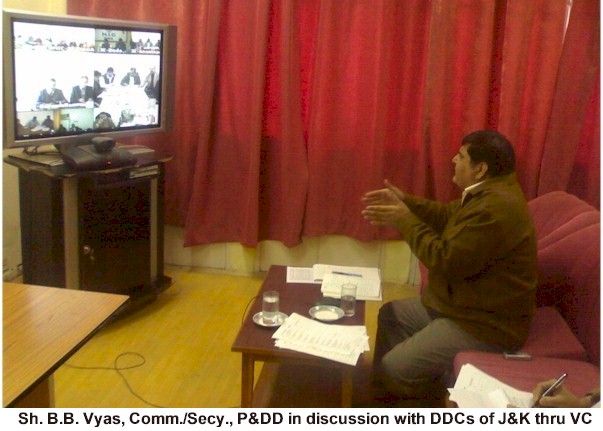
Commissioner/Secretary, Planning & Development Department, Shri B.B. Vyas, IAS reviewed the progress of development issues with all the District Development Commissioners (DDCs) of J&K through Video Conferencing on 24.10.2009, keeping in view the commencement of PM’s visit to J&K. He addressed all the DDCs from VC Studio of NIC J&K Civil Secretariat Srinagar and discussed issues pertaining to development schemes running in the districts. All the DDCs except Leh & Kargil of J&K have participated in this VC Session from the respective/nearby districts itself. The VC session was lasted for almost 2 hours. Mr. Vyas appreciated the efforts of NIC for conducting the VC Session very successfully.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


