SUGAM makes an Impact All Over Rajasthan
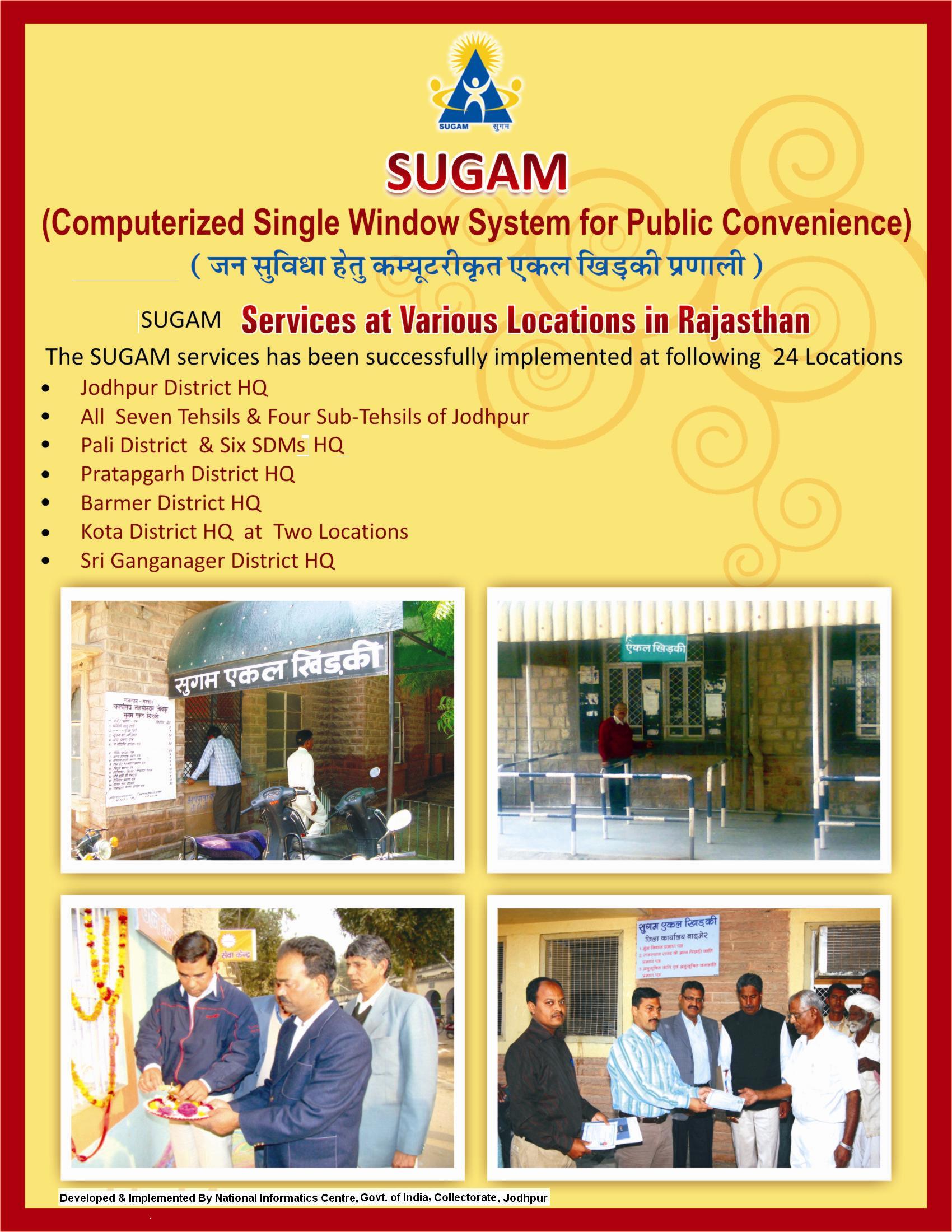
The SUGAM Project: a Government to Citizen (G2C) special from Jodhpur district in Rajasthan ia a single window system set up by the District Collectorate at NIC Jodhpur to provide multifaceted services to the citizens through a a single window which included domicile, SC/SC, State and centre level- certificate, Ration card etc. All the reports and certificates are printed in Hindi . It has proven to be a boon for th citizens of the district for delivery of citizen services at on point. The software has been developed by H.S. Gehlot by DIO Jodhpur & TD and Ravi Mathur DIA Jodhpur. Two new options : permission letter for birth –death certificate and renewal of arms licence has been added in the previous years. State informatics Officer & Sr. Technical Director NIC Indu Gupta informed that “ the project has been replicated throughout the state and has proven to be very useful” . The single window project has been taken up in priority by the state government for implementation all over the state. Many officials have visited jodhpur for the training on the project and to learn the implementation features. The Microsoft platform/product/technology used include VB, .Net , MS-Access , Crystal reports etc. The project was launched in December 2003 with a provision of delivering two services domicile certificate and caste certificate.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


