Capacity Building on Jal Shakti Abhiyaan "Catch the Rain, Where it Falls, When it Falls" (JSA: CTR) Portal at Dhamtari, District, Chhattisgarh

JSA:CTR campaign was launched by Hon’ble Prime Minister on 22nd March, 2021. As per the instructions of Jal Shakti Mantralay, GoI, every district must prepare inventory of existing water bodies within district using the JSA portal.
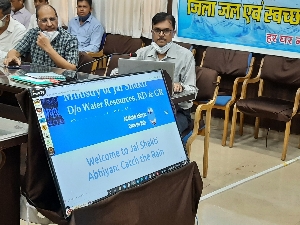
For the smooth implementation of Jal Shakti Abhiyaan, a detailed training session on JSA Portal for all government agencies and departments has been imparted by Shri Upendra Singh Chandel, DIO, NIC Dhamtari on 25th September 2021.
The training was organised at District Collectorate Meeting Hall at Dhamtari under the chairmanship of Shri Padum Singh Alma (IAS), Collector & District Magistrate. About sixty participants from various line departments were present.
After brief introduction of JSA portal, step by step workflow of entire module was presented by NIC and detailed online demonstration was given to the officials. Several important features related to the online portal and use of JSA Mobile application were covered during the training.
After completion of the training program doubt clearing session was also conducted.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


