Honourable LG J&K felicitated DIO NIC District Centre Jammu
Jit Raj, Jammu and Kashmir
jit[dot]raj[at]nic[dot]in
| Feb 1, 2021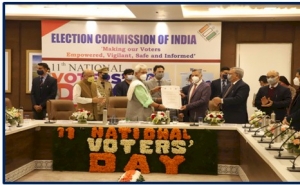

Hon’ble Lieutenant Governor of Jammu and Kashmir Union Territory awarded a Certificate of Appreciation to District Informatics Officer NIC District Jammu Mr. Sanjay Gupta for his Technical Interventions during the Electioneering Process on 11th National Voter Day held at Nirvachan Bhawan Jammu on 25th January 2021
Among others who were present on the occasion were Advisor to Hon’ble Governor Sh. Farooq Khan, Worthy Chief Secretary Shri B. V. R. Subrahmanyam IAS, State Election Commissioner Sh. K.K. Sharma, Sh. Hirdesh Kumar, IAS, Chief Electoral Officer, J&K and other Officers.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


