Hon'ble Chief Minister, Himachal Pradesh Launches CM Office ICT Initiatives and Constituency Profiler

Sh. Jai Ram Thakur, Hon'ble Chief Minister, Himachal Pradesh launched three ICT initiatives of Chief Minister office on 6th January 2021 in the virtual presence of 34 Hon'ble Members of Legislative Assembly at Shimla. The Chief Minster expressed the hope that with the launch of these initiatives, the citizens and MLAs will benefit as they will get important information online and development of assembly segments can be monitored in a better manner.
Sh. Suresh Kashyap, Hon'ble Member of Parliament, Shimla, Sh. J.C. Sharma, Principal Secretary to Chief Minister and Dr. R.N. Batta, Advisor to CM were present on this occasion. Two of these initiatives namely, Front Office Desk and Constituency Profiler are developed by NIC Himachal Pradesh.
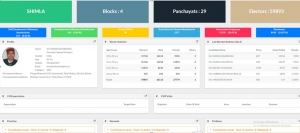
SIO, NIC Himachal Pradesh gave presentations on the two initiatives highlighting the points covered like, online submission of requests for appointments, meeting/ tour/ launch/ event calendar, Dos/Proposals monitoring at State/ GOI level etc. At the constituency level, details of ongoing work details in constituency, profile of electors, beneficiaries, Government employees, pensioners, schemes, MoUs, important projects, problems, demands, expectations and priorities can be monitored with focus on all round time bound development.
Hon’ble Chief Minister desired to have special training-cum-demo programs for the MLAs so that the software is properly utilized, which is accessible from the Him Pragati Portal. The software solution has been developed by NIC HP by integrating services from different software implemented in State.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


