Indepdence Day Honours for DIO Hamirpur, Himachal Pradesh

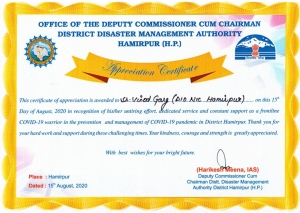
Sh. Vinod Kumar Garg, Scientist-E/DIO Hamirpur, HP has been awarded the “Certificate of Appreciation for COVID-19 Warrior” in recognition of the services provided during the COVID-19 pandemic.
The certificate has been awarded by Sh. Rajinder Garg, Hon’ble Minister, Food, Civil SupplieS & Consumer Affairs, Himachal Pradesh,. Sh. Narinder Thakur, Hon’ble MLA Hamirpur Assembly Constituency and Sh. Harikesh Meena, IAS, Deputy Commissioner Hamirpur Sh. Arjit Sen Thakur, IPS, Superintendent of Police Hamirpur were present on the occasion. The District level 74th Independence Day in district in Hamirpur, Himachal Pradesh was celebrated on 15th August, 2020 at Government Sr. Sec. School (Boys) Ground.
The appreciation certificate has been awarded in recognition of the services delivered for the management of the COVID-19 District Control Room, Call Centre, Covid ePasses, End-User Trainings on RATI/RT-PCR Mobile Apps, Video Conferences with the field level officers/officials in the district and miscellaneous I&CT support on various COVID-19 related activities. During this period, NIC has played a vital role as a technology partner for the containment of the Corona Virus. Sh. Vinod Kumar, DIO and Sh. Anurag Gupta, ADIO along with FMS staff in District have provided crucial ICT services during the Covid19 containment period in District Hamirpur. The services provided by the NIC have been greatly appreciated by all.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


