CSI SIG eGovernance Award 2019 for Digital transformation solution towards Distribution and monitoring of Agricultural Implements

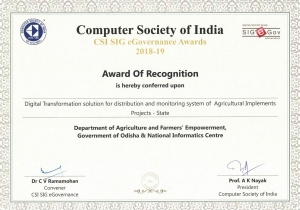
Agriculture team of NIC , Odisha and Department of Agriculture and farmers’ Empowerment, Govt of Odisha jointly received the CSI SIG eGovernance Award of Recognition from Shri Tusharkanti Behera, Hon’ble Minister, Electronics & IT, Odisha for the Project ‘Digital Transformation solution for distribution and monitoring system of Agricultural Implements and increasing Irrigation Potential through electric and solar’ on 17th January 2020 as part of the 53rd CSI Annual Convention at KiiT University, Bhubaneswar, Odisha
This online system facilitates the error free distribution of farm machinery, execution of PLIP (Private Lift Irrigation points) through electric power, installation of solar system for pump set through solar power and finally transfer of entitlements and benefits directly to the beneficiary’s Bank account as well as to the OREDA account.
The program cuts across all beneficiaries which include large farmers, small farmers, marginal farmers and share croppers. This streamlines the process and trims the number of intermediaries and delays in the system. All the central and state sponsored schemes can be monitored and implemented effectively by the department at a much higher level. It enables seamless service delivery of G2C & G2G.
This initiative has been coordinated by Ms. Sarita Sahoo, STD with the support of Agriculture team of NIC, Odisha and under guidance of Ms. Pratibha Singh, DDG & SIO, Odisha.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


