Governance
Nagaland State Moving towards a Digitized Era
Since its inception in the year 1989, NIC Nagaland has been playing a pivotal role in the Government of Nagaland in promoting ICT Infrastructure and e-Governance Applications for providing efficient and transparent government services through e-Governance. Its Computer Communication Network NICNET...
CARINGS Child Adoption Resource Information and Guidance System
CARINGS (Child Adoption Resource Information and Guidance System) portal is an e-governance system on adoption designed, developed, deployed and maintained by the National Informatics Centre. It ensures transparency in the adoption process, increases accountability of implementing agencies, creates...
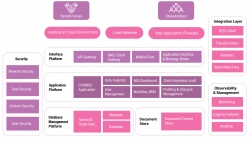
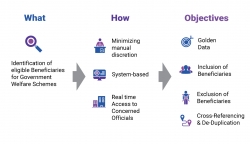
Unified Data Hub Empowering Proactive Governance through Integrated Solutions
UDH has established an adaptable system for validating and eliminating duplicate beneficiaries. Presently, it encompasses Puducherry residents and their enrolled schemes, incorporating 24 departments and 150 central and state schemes. Its scalability allows seamless integration with new schemes. The...
Nashik, Maharashtra Setting a benchmark in delivering efficient ICT solution and services
Established in 1989, NIC Nashik is a leading ICT service provider for Divisional and District administration, enabling efficient G2G and G2C services. It has executed numerous state and central government e-Governance projects, including locally developed web applications like RRIS and eTapal. These...
Hardoi, Uttar Pradesh Enabling the Growth of Digital India through ICT Solutions
NIC Hardoi has been assisting the district administration in promoting Digital India in the district for a number of years by developing and implementing a number of in-house initiatives, such as the Saakshi (Summon Information Management System), Todarmal Application, and Sampada Application. One...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


