Automation
Himachal Integrated Registration Information System (HIMRIS)
Registration of deeds is the first and the most critical step in acquiring title to land or property and thus, assumes significance for those who are involved in these transactions. The registration of these transactions is mandatory to make them legal, otherwise ownership rights cannot be claimed/transferred....
TrackChild2.0 : National Tracking System for Missing and Vulnerable Children
The portal TrackChild 2.0 - National Tracking System for Missing and Vulnerable Children (www.trackthemissingchild.gov. in) is dedicated to the cause of tracking missing and vulnerable children. It holds the national database of children who are reported as missing or found along with those...
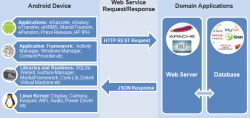
Android Mobile Apps to Supplement Web Content
India has the fastest growing telecom network in the world credited to its high population and development potential. The total number of telephones in the country stands at 957.61 million, while the overall teledensity has increased to 76.75% as of 30th September 2014. The total number of mobile...
Goa Excise Management System (GEMS)
GEMS is Government to Business (G2B) initiative of Department of Excise, Government of Goa, aimed at achieving good governance and paperless office using ICT tools. The project was entrusted with NIC in October 2013, to develop a complete web based workflow application providing end-to-end solution...
eVisitor: IT Solution for Visit Management
eVisitor, a web based application system developed by NIC is a citizen service to facilitate submission of online requests for visiting Officers of Ministries/Departments located at various Bhavans. Home Page of the Ministry website, directs the visitor to eVisitor site ie., http://MyVisit. gov.in....




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


