ICT in States
AEBAS in School Education - Tamil Nadu Govt. strides ahead with the best use of ICT
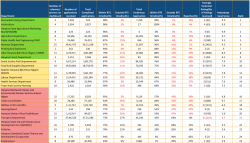
Government of Tamil Nadu has taken initiative to implement Aadhaar Enabled Biometric Attendance System (AEBAS) in Government and Government Aided Schools in Tamil Nadu. Tamil Nadu state consists of 120 District Educational Offices which comprises of 45,614 schools employed with 3.15...
Uttarakhand Teachers Eligibility Test (UTET) Online - Exam Management System-2019
Till 2018, the entire process UTET was carried out manually by the Uttarakhand School Education Board. Understanding the complications and challenges of the manual system, NIC- Uttarakhand proposed Department of School Education, Uttarakhand to design and develop a computerized system enabling automation...
HIMACHAL PRADESH: Leveraging ICT for better e-Governance and delivering enhanced services to citizens
NIC Himachal Pradesh has developed two national level products of Manav Sampada and Mid Day Meal Automated Reporting System, which are replicated in 17 other states. The Competency Centre for Mobile App Development, NIC Himachal Pradesh has developed 64 Apps on Android and 26 on iOS platforms,...
ODISHA STATE: Empowering Digital Odisha with 5Ts Mantra
The advent of National Data Centre (NDC) in Bhubaneswar by the Government of India and the adoption of 5Ts (Technology, Teamwork, Time, Transparency and Transformation), the new concept of service delivery by the Government of Odisha, jointly give a tremendous thrust on e-Governance service delivery...
Antyodaya SARAL Haryana: A unified platform ensuring hassle-free & time-bound delivery and tracking of G2C services in the State
Having implemented Antyodaya SARAL, Haryana is the first state in the country to integrate so many schemes and services on one platform. The powerful solution developed by NIC Haryana has channelized the process of bringing about a fundamental behavioral change in the way the government functions, and...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


