ICT in States
ODISHA STATE: Empowering Digital Odisha with 5Ts Mantra
The advent of National Data Centre (NDC) in Bhubaneswar by the Government of India and the adoption of 5Ts (Technology, Teamwork, Time, Transparency and Transformation), the new concept of service delivery by the Government of Odisha, jointly give a tremendous thrust on e-Governance service delivery...
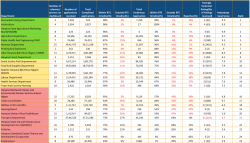
Antyodaya SARAL Haryana: A unified platform ensuring hassle-free & time-bound delivery and tracking of G2C services in the State
Having implemented Antyodaya SARAL, Haryana is the first state in the country to integrate so many schemes and services on one platform. The powerful solution developed by NIC Haryana has channelized the process of bringing about a fundamental behavioral change in the way the government functions, and...
Integrated Financial Management System (IFMS) An end-to-end system for Financial Management in the Government of Kerala
NIC Kerala has developed and implemented various application modules in the IFMS Project. As part of the IFMS project, smooth and successful integration has been achieved with various stakeholder applications such as SPARK (HR Management System) and EMLI (Effective Management of Letter of Credit Issuances).
MADHYA PRADESH : Pacing up with technological advancement to lead ICT transformation for efficient e-Governance
NIC Madhya Pradesh, The Cyber Gateway of the State, was set up in Bhopal in 1988 to play a catalytic role in promoting informatics culture and providing ICT services to Government Departments and Organizations. The roads from rich historical past are passing by the present developing State...
GOA STATE : On a progressive path to become the next IT Hub of India
NIC Goa State Centre is the leading solution provider of ICT services in the State. Aimed at better e-Governance, the initiatives by NIC Goa have earned several prestigious accolades to its credit. South Goa is a unique District in India where a complete Data Centre is provided by the District Magistrate.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


