ICT Initiatives
Jodhpur District - ICT Shines Over The Sun City
Jodhpur, the Sun City is the second-largest city in India and officially the second metropolitan city of the state. Jodhpur is a popular tourist destination, featuring many palaces, forts and temples, set in the stark landscape of the Thar Desert. It is popularly known as Blue City and Sun City among...
NGT Online Portal: An electronic smart court to address environmental protection issues.
Facilitating an effective, IT based and less-paper Grievance Redressal System to handle environmental disputes involving multi-disciplinary issues, the NGT online solution has enabled digitization of all the court documents that get stored in the repository (Document Management System), thereby maintaining...
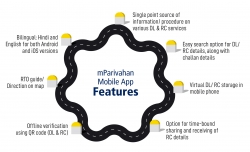
mParivahan: A citizen-centric transport solution enriched with latest technologies
mParivahan Mobile App has become an integral part of the transport ecosystem in a very short duration and gained significant mind share of the citizens, government and businesses alike. By virtue of its huge popularity and features like Virtual DL & RC, QR code-based verification etc., it...
eCourts Services : Transforming Judiciary for Effective Justice Delivery
eCourts, a Mission Mode Project of the Government of India, has set an example of successful eGovernance project reaping rich dividends to litigants and citizens of the country. The eCourts project was conceptualized on the basis of the National Policy and Action Plan for Implementation of Information...
National Power Portal : Providing comprehensive framework for Power Sector data capture and dissemination
National Power Portal (NPP) is a unified system developed for Indian Power Sector to facilitate online data capture/ input (daily, monthly, annually) from generation, transmission and distribution utilities in the country and disseminate the power sector information (operational, capacity, demand,...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


