ICT Initiatives
Appscape
Tapping the potential of advanced technologies, e-Governance provides services through the use of computerization and replaces traditional way of working with paperless work. Mobile governance (m-Governance) is a subset of e-Governance to deliver services for different government channels, namely G2C,...
JIND DISTRICT, HARYANA : Delivering innovative ICT Solutions to foster excellence in e-Governance
The NIC District Centre has enhanced accessibility and delivery of various government services to the citizens. Apart from dedicated ICT support to the District Administration, NIC Jind has pioneered many successful ICT initiatives that have improved the citizen experience.
e-NIYANTRAN : Online Time Card System to save the migrating wildlife of Kaziranga National Park, Assam.
e-Niyantran will replace the existing Manual Time Card System of regulating the vehicular movement on NH-37, the highway which runs parallel to the southern boundary of Kaziranga National Park. The system would help avoid accidental death of wild animals while they cross the highway, especially during...
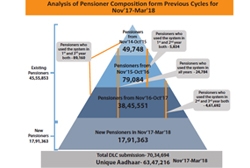
JEEVAN PRAMAAN Digital Life Certificate
Since its implemention in 2014, over 1.6 crore DLCs have been submitted by over 90 lakh pensioners. 3.01 lakh DLCs were submitted in a single day on 13th Nov, 2017. Peak utilization of the system was observed as 1,205 DLCs per minute on 9 Nov, 2017 at 11:36 AM. Jeevan Pramaan ecosystem has...
e-HRM System for Government by NIC
This recently launched Application enables creation of e-Service book of employees from physical service book and automate the updation of e-Service book. This makes day-to-day processing of various records of employee possible, resulting in real time updation of servicebook and uniform implementation...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


