e-Services
Single Window Clearance Systems implemented at DC Office Jammu
National Informatics Centre District Centre Jammu has taken a lead in implementation of Web Based Single Window Clearance Systems in Deputy Commissioner Office Jammu. This system will help in fixing accountability on the part of individuals at each level and for providing better services to citizens...
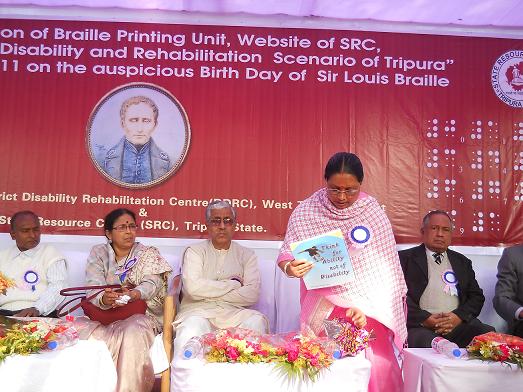
Service towards the Disbaled Persons of Tripura
Hon'ble Chief Minister of Tripura Shri Manik Sarkar inaugurated the website of State Resource Centre of the Disabled Person on 4th January 2011. Often due to lack of consolidated information Disabled person have been deprived of Government assistance. Under the able direction and guidance of...
Inauguration of e-service for Non-Government Pensioners of West Bengal by Chief Secretary
Work flow based processing of Pension Files for Non-Government Pensioners including School Teachers and Non-teaching staff, Employees of Municipalities, Employees of Panchayati Raj Institutions and those of other organizations has been going on for the past few years in the Directorate...
eStepin : Online Token booking for Registration Offices, Maharashtra
eStepin : Online Token booking for Registration Offices, Maharashtra. Â Adieu to queues, property registration is just a click away, Endeavouring to add speed and transparency to land records/ property registration, the State Stamps and Registration Department has put in place, eStepIn,...
E-Governance Module at LBSNAA, Mussoorie
An E-Governance Module was organized for IAS Professional Course Phase – I (2009 Batch) at Lal Bahadur Shastri National Academy of Administration, Mussoorie. A session on “Role of NIC” was delivered during the module by Dr. Shefali Dash, Deputy Director General, NIC HQ, New...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


