Service towards the Disbaled Persons of Tripura
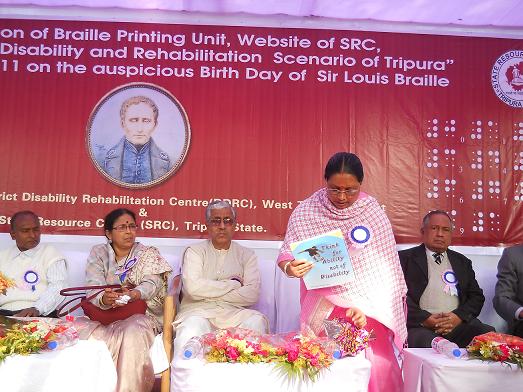
Hon'ble Chief Minister of Tripura Shri Manik Sarkar inaugurated the website of State Resource Centre of the Disabled Person on 4th January 2011.
Often due to lack of consolidated information Disabled person have been deprived of Government assistance. Under the able direction and guidance of Hon'ble Chief Secretary Shri S.K. Pandey, an application, Physically Challenged Persons Information System(PCPIS) was launched which links the major departments like Social Welfare, School Education, District Disability Rehabiliatation Centres, Employment Exchange for updating the information of a Disbaled person. The PCPIS application delivers instant generation of the Disabled Certificate on medical chekup, which in turn is served to to the citizen.
The SRC website is an added service to the PCPIS. It aids in monitoring of multiple activities of the stakeholders and in decision making process of the Government.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


