Articles
Changing the Paradigm of Mapping - UAV/ DRONE with AI/ ML Innovations
Drone enables topographic surveys of the same quality as highly accurate measurements collected by traditional methods, but in a fraction of time. This substantially reduces the cost of a site survey and efforts. Today drones coupled with Artificial Intelligence (AI) and Machine Learning (ML)...
Uttarakhand Teachers Eligibility Test (UTET) Online - Exam Management System-2019
Till 2018, the entire process UTET was carried out manually by the Uttarakhand School Education Board. Understanding the complications and challenges of the manual system, NIC- Uttarakhand proposed Department of School Education, Uttarakhand to design and develop a computerized system enabling automation...
AEBAS in School Education - Tamil Nadu Govt. strides ahead with the best use of ICT
Government of Tamil Nadu has taken initiative to implement Aadhaar Enabled Biometric Attendance System (AEBAS) in Government and Government Aided Schools in Tamil Nadu. Tamil Nadu state consists of 120 District Educational Offices which comprises of 45,614 schools employed with 3.15...
Gujarat CM Dashboard - Enabling government machinery for strengthening good governance
The system first of its kind was an innovation in terms of accessing data from all e-Governance applications of the State of Gujarat and providing the same for monitoring against defined KPIs. In the reverse, CMO could drill down to the granular level on the fly for red-flagged items and intervene...
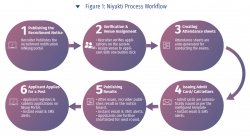
Niyukti - A one stop recruitment solution for the Government of Assam offered as a service
Since its inception in the year 2017, Niyukti has quickly evolved as a widely used recruitment solution in Assam Government. Its USP lies in the fact that it is offered as a service to the recruiting agencies, thereby allowing them to quickly onboard with a recruitment process in no time. Already...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


