eHimBhoomi Workshop for Revenue Officers of District Solan, Himachal Pradesh

A half day eHimBhoomi awareness workshop was held at Solan on 15th November 2016 for the Revenue Officers of the District Solan. Sh. Rakesh Kanwar, the Deputy Commissioner, Solan had desired to hold a half day demonstration of the Integrated eHimBhoomi features, software, mobile apps for the Revenue Officers of the District Solan during their monthly meeting. Sh. Ajay Singh Chahal, SIO, Vimal Kumar Sharma, Scientist-D, Sh. Ashish Sharma, Scientist-B and Sh. Parveen Kumar, Scientist-B visited Solan while Sh. Sanjeev Kumar, DIO, Solan coordinated the awareness workshop at Solan.
Sh. Rakesh Kanwar, IAS, Deputy Commissioner, Solan informed the participants about the need for making them aware of the new technological advancements taking place in various revenue software were felt.
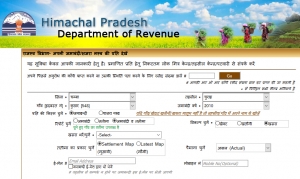
During the demonstration of eHimBhoomi, the SIO NIC Himachal elaborated various salient features of 'Integrated eHimBhoomi' and value additions done in the last two years viz. incorporation of Digital Signature, Web enabled mutation module, Integration with other Revenue Application softwares, map solution (Bhunaksha), Aadhaar seeding in Himbhoomi software and mobile App named mHimBhoomi. He stated that with its implementation, there is a phenomenal 400 percent transactional growth in citizen services rendered through Common Service Centre/Lok Mitar Kendra, Sugam Centres in the State. The SIO Himachal informed the participants about the future plans which are being initiated by NIC Himachal.
The Revenue Officers of the District Solan were given a demonstration of the different Mobile Apps launched by NIC Himachal for various departments under different platform. Usage of these Apps to fetch information was demonstrated by Sh. Ashish Sharma, System Analyst from NIC Himachal State Centre.
During deliberations, the suggestions put forwarded by Revenue officers were discussed in detail and the Deputy Commissioner informed that matter will be taken up with the appropriate authority and amendments if required, will be incorporated in these software accordingly.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


