Training cum Workshop on CAPA (College Accounting Procedure Automation) Project
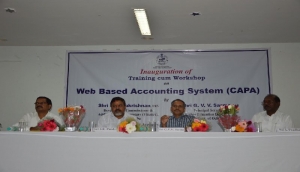

Week long training cum workshop programme on pilot implementation of CAPA (College Accounting Procedure Automation) project was organized for the Principal, Accountant and Accounts Bursar of Non-Government Aided Colleges under Govt. of Odisha from 30th January 2016 to 9th February 2016 at KOEL Campus of KIIT, Bhubaneswar, Odisha. The workshop was formally inaugurated by Shri G.V.V Sarma, IAS, Principal Secretary, Department of Higher Education (DHE), Govt. of Odisha and Shri S. K Panda, DDG & SIO, NIC, Odisha State Centre in presence of officials from Finance, Directorate of Local Fund Audit and Higher Education Department, Govt. of Odisha.
In his inaugural address Shri S. K Panda, DDG & SIO thanked the Finance & Higher Education Department, Govt. of Odisha for entrusting on NIC to develop the CAPA Portal, which will be useful for colleges to maintain their day to day finical transactions and preparation of accounts related documents to meet audit requisites. This system will bring uniformity in accounting of all the colleges.
Shri G.V.V Sarma, IAS , Principal Secretary , Department of Higher Education, Govt. of Odisha, applauded NIC for making pilot implementation of CAPA in schedule time. He specially thanked NIC for organizing the workshop and advised the participants to make optimum use of this week long training programme.
On morning session of the workshop, general concepts and work flow of CAPA was explained to the participants by Smt. Minati Sahu, TD, Shri Bebin Mishra , SO/E-SB from NIC, Shri S. Sarangi from Directorate of Local Fund Audit along with officials from DHE. The post lunch hands-on sessions were organized in which the participants accessed the CAPA portal with their valid user-id & password to monitor the day to day activities and audit program execution.
The whole training program was carried out by Shri Dillip Kumar Jena, TD, Smt. Minati Sahu, TD along with Shri Bebin Mishra, SO/E-SB from NIC, Bhubaneswar. In the concluding session, the finance team interacted with the participants to get their feedback. The week long workshop concluded with very positive & constructive feedbacks from all the participants.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


