HARYANA: SMS and Web based e-Dashboard Launched for Lok Sabha Election-2014

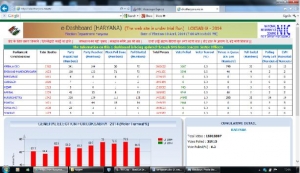
The e-Dashboard is a web based software developed at NIC-Hisar District unit of NIC Haryana in coordination with the O/o Chief Electoral Officer, Haryana and NIC State Project Coordinators for Elections.
The e-Dashboard software is an SMS based tool for the poll monitoring & it automatically updates the information relating to various Events at e-Dashboard through SMS gateway of NIC. At assembly level the supervisors /sector officers are assigned 15-20 booths each & their registered mobile nos. are mapped with booth NOs/Booth codes. The mapping of mobile Nos. with booths Nos. ensures that the SMS are sent by authorized officers only and each supervisor is accountable for the booths allotted to him.
Sh. Ghan Shyam Bansal DDG-Cum-SIO Haryana explained the functionality & Technical aspect of the software to media. Sh. Surjeet Singh, TD, NIC Haryana & Sh. Pardeep Kaushal ,TD NIC Haryana gave the live Demo of the software.
The Supervisors shall visit the allotted booth, collect the information & send the SMS to update the information on the E-Dashboard.
The software automatically calculates the voter turn out percentages & shows the pictorial representation of the data in the form of bar chart for different events, parliamentary constituency wise & Assembly constituency wise. It also shows comparison chart of voting percentage between 2009 lok sabha polls and current polls.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


