Inauguration of C-FRO module under IVFRT project at Puri, Odisha

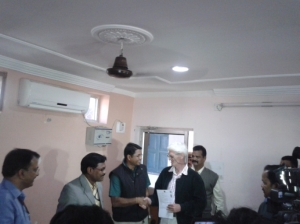
The C-FRO module for Puri district of Odisha was inaugurated on 1st Feb 2014. Shri Anup Sahoo, IPS, SP and FRO Puri, welcomed all the guests and dignitaries to the event and the program was formally inaugurated by Shri Lalit Das, IPS, Special Secretary to Home Department, Govt. of Odisha.
Dr. B. N. Shetty, DDG, NIC New Delhi explained in detail the prospective and benefits of the project. Shri N. S. Rawat, PSA, NIC New Delhi explained detail about the various modules to be used at the district level.
Shri Anup Sahoo, IPS, SP & FRO, Puri delivered the first computer generated Certificates of Puri to foreign nationals present on the occasion.
Shri Biswanath Panda, DIO, NIC, Puri, Shri Arun Jayshankar and Shri Vikash Khatri from NIC New Delhi coordinated for the overall success of the program.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


