Haryana: Launch of Mobile Phone Application for Online Display Board by Honorable Chief Justice
On 24th September 2013, Honorable Chief Justice Sanjay Kishan Kaul launched the ‘Mobile App’, which is free to download for android or Java-based mobile phones. By using this App, one can watch the live display to know the status of the cases being taken up in the various Courts. The Supreme Court’s e-Committee has got developed a mobile application for online display-board, which has been customized for the High Court.
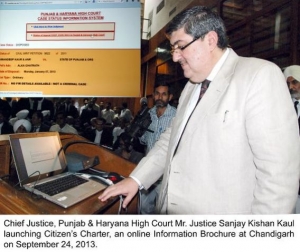
To improve Justice Delivery System and to help avail various facilities available in the premises of the Punjab and Haryana High Court for the litigants and general public, the Chief Justice Sanjay Kishan Kaul also released "Citizen’s Charter" of the High Court. The charter has also been uploaded on the High Court’s website — www.highcourtchd.gov.in.
Another application — Case Management Module —has also been launched which would help advocates to maintain an "e-Diary" of their cases which would provide complete status of a case by linking it to the "Case Status Module". It would be a Cause List of particular advocate giving complete details of the cases including complete judgments of his decided cases. Advocates desirous to avail this facility would have to apply to the High Court, procedure regarding which has been put on the website.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


