Haryana: Inauguration of e-Disha Centre by Hon'ble Chief Minister in Sonipat
Poonam Gupta, Haryana
poonam[dot]g[at]nic[dot]in
| Aug 29, 2013
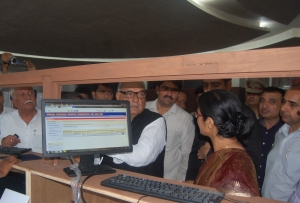
Hon’ble Chief Minister, Shri Bhupinder Singh Hooda has inaugurated newly established e-Disha centre on 15th August, 2013. During the inauguration Deputy Commissioner Sonipat, Sh. Chander Shekhar and other senior officers were also present. The e-Disha center has been established in newly constructed Mini Secretariat of Sonipat district with 14 numbers of counters to provide G2C services. The citizens will get the services like Driving License (Learner/Permanent/Renewal etc.), Registration of Vehicle (New Vehicles/Transfer of Ownership/ Duplicate etc.), Issue of Conductor License, Forms (Filled/Blank), Public Grievances (Harsamadhan) etc.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


