Online System for monitoring Primary Schools in Aligarh, Uttar Pradesh
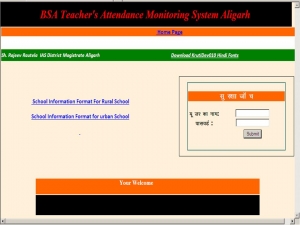

An online system has been designed and developed by NIC, Aligarh to monitor the prevailing condition of primary schools in the district. The system keeps record of available staff, attendance of students, mid-day meal, uniform distribution, condition of toilets, hygiene, boundary wall, electrical connection, infrastructure and disbursement of scholarship of all the district primary schools. The information is updated electronically on daily basis by the office of BSA (Basic Shiksha Adhikari) and Assistant BSA and can be accessed by the District Magistrate, Chief Development Officer and other senior officials of Education Department. The web based system seeks to remove the anomalies prevalent in the management of primary schools and ensure a transparent working environment under the supervision of higher authorities. The online system http://aligarhadmin.in was inaugurated on 1st of April 2013 under the guidance of District Magistrate Shri Rajeev Routela.
In order to provide data security and ensure authenticity of data user-id and password have been provided to all the BSA & Assistant BSA for uploading of data on the website. A training session was also organised at NIC, Aligarh for BSA staff to ensure proper utilization of the system and make officials aware about its functions.
The online system will ensure transparency, improve the conditions of primary schools and will definitely help in removing the anomalies in the scholarship distribution programme of the state government




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


