Haryana: Dynamic Integration of Property Registration, Land Records & Cadastral Maps Project Received CSI - Nihilent e-Governance Award 2011-12

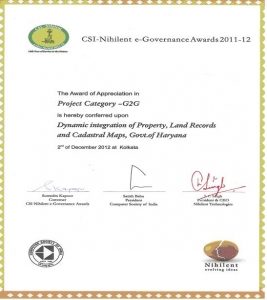
The Haryana’s project Dynamic Integration of Property Registration, Land Records & Cadastral Maps has received CSI-Nihilent Awards 2011-12, under Projects Category, on December 02, 2012 at Science City Kolkata. The award was presented at the 47th Annual Convention of Computer Society of India, which organized International Conference on Intelligent Infrastructure, at Science City, Kolkata, during December 01-02, 2012. The award was presented by Padma Shri Prof P.V.S. Rao.
Chief Secretary Haryana Sh. P.K.Chaudhary congratulated SIO Haryana Sh. G.S.Bansal for receiving this prestigious award.
In Haryana, the workflow based Property Registration Information System (HARIS) and Land Records Information system (HALRIS) have been dynamically integrated to reflect the impact of registration of Land on Jamabandi and to provide authenticated ROR (Nakal of Record Of Right) services to the citizens. The digitized Cadastral Maps of 120 Jamabandies of Ambala district has further integrated with textual Records-of-Rights. This integration is an end-to-end solution for delivery of a bucket of e-services to the citizens, (which includes issuing of computerized RORs along with digitized map of the land, Registration of documents, Mutations, calculation of stamp duty, on-line photo capturing of buyers, sellers, witnesses etc), with greater transparency, authenticity and ease of e-service delivery.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


