Launch of Online Issue of C and F Forms for Commercial Taxes Department, Tamilnadu
Objectives
The system facilitates the authorized dealers to file online application and generation of C and F form by logging into the Web Site of Department of Commercial Taxes, Tamil Nadu. C and F Forms are generated based on the Monthly Returns filed with Annexures by the Dealers. For this purpose, a separate Annexure I-A has been introduced in e-Return with necessary amendment in the Act. Dealer should file Monthly Returns with Annexure I-A which consists of transactions Inter-State purchase and Inter-State transfer of goods in the prescribed format. The C Form is for Inter-State purchase transaction and F Form is for Inter-State stock transfer of Goods. The Dealer can generate C and F Form online without visiting to the Circle Office.
Features of Online issuance of C and F Forms
• Filing of e-Return with Annexure I-A.
• Form Generation is based on Monthly e-Returns.
• Seller TIN Verification against TINXSYS online.
• Commodity Code filtering based on CST Registration Certificate.
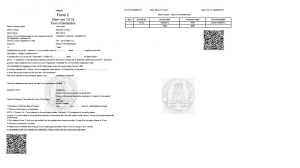
• Printing of Online Forms with Unique C and F Form Number.
• No Approval or Signature is required for generation of Online Forms.
• Cancellation and Re-generation of Online Forms with the approval from Commercial Tax Officer.
• 24 * 7 online generations of online Forms.
• 2D Bar Code for security and verification of online Forms.
• Water Mark for Online Forms.
• Various MIS Reports for Department Officials for effective monitoring
Implementation Status
• Government has issued GO’s for Annexure I-A submission Vide G.O. No.110 Dated 10.08.2012.
• The service launched on 01/11/2012.
• More than 7586 C Forms and 270 F Forms generated since Launch.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


