GePNIC presentation at Garden Reach Shipbuilders and Engineers Ltd, (GRSE), Kolkata, Ministry of Defence by eProcurement Team, NIC, Orissa
Garden Reach Shipbuilders and Engineers Ltd, (GRSE), a “Mini Ratna Category-I” PSU under the Ministry of Defence, Government of India , is among the leading shipyards in the country. It builds wide range of ships from modern Warships to sophisticated Commercial Vessels, from small Harbour Craft to fast and powerful Patrol Vessels. It is among the few shipyards in the world with its own Engineering and Engine Manufacturing divisions.
Being motivated by the move of Hindustan Shipyard Limited (HSL), Visakhapatnam, to implement GePNIC, GRSE also approached NIC for presentation on GePNIC with the intention of bringing transparency & efficiency in their procurement process.
Accordingly, NIC Orissa eProcurement team, Shri Tapan Prakash Ray, TD & Shri Nihar Ranjan Biswal, PSA, visited GRSE, Kolkata on 13th July 2011. The team presented GePNIC features, implementation status in various states and PSUs, process flow, advantages of adopting the software, security aspects etc to the top management of GRSE, headed by Rear Admiral K. C. Sekhar, Chairman-cum-Managing Director. He expressed his desire to implement the eProcurement system of NIC at the earliest possible timeframe. The queries raised by some of the board members were discussed in detail by NIC team.
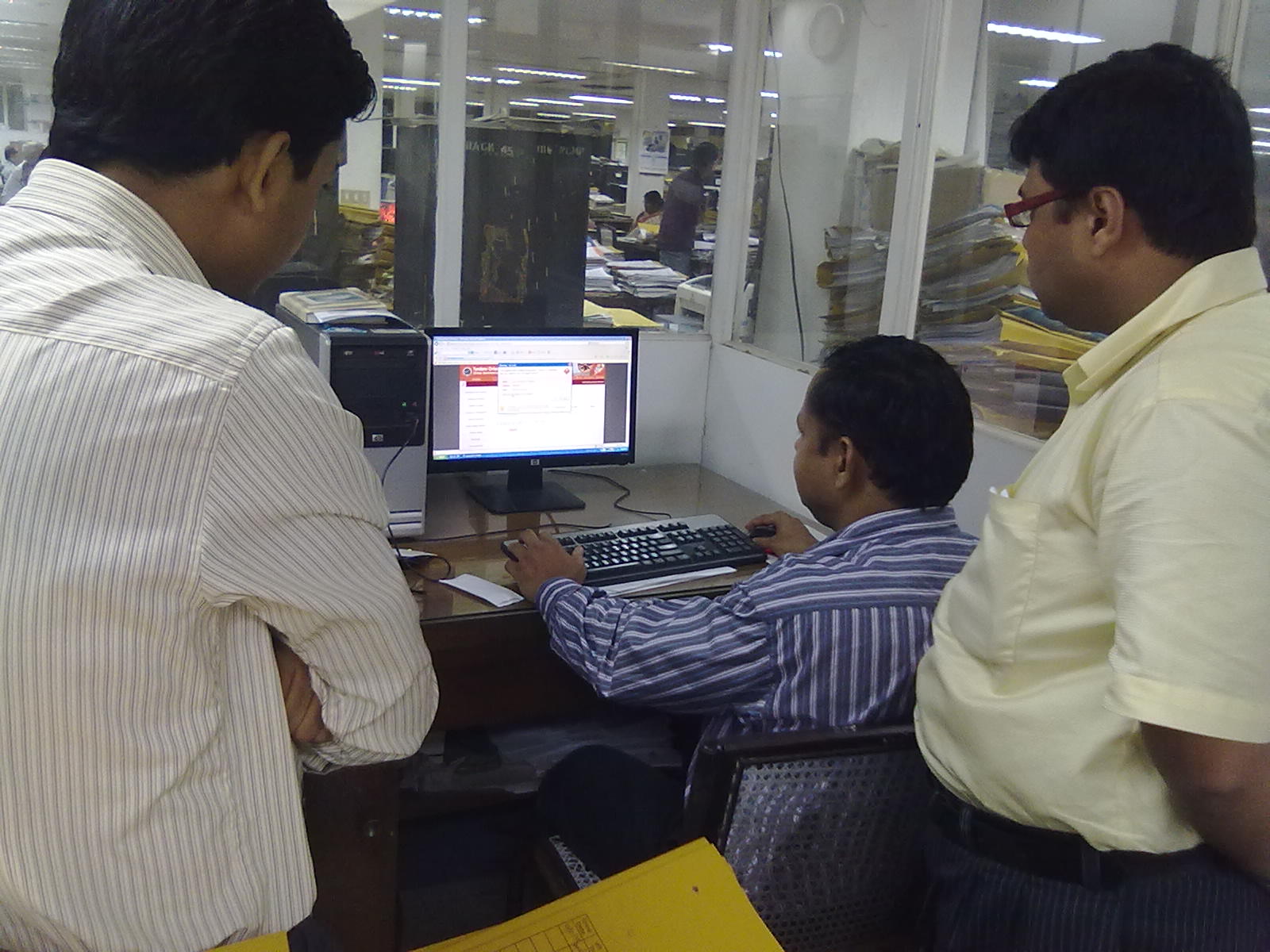
After the presentation, a live flow of the application was demonstrated to the procurement team of GRSE. GRSE management appreciated the presentation by the NIC team and has expressed the desire to implement the solution primarily for Goods module of GePNIC apart from Works and Services.
-e-Procurement team, NIC, Orissa




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


