Review of Progress of Schemes of District Kaithal by Sh. Naveen Jindal, MP, Kurukshetra
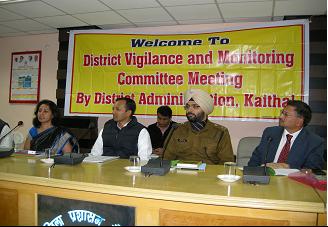
District Vigilance and Monitoring Committee meeting was held on 13.12.2011 at Mini Secretariat, Kaithal under the chairmanship of Hon’ble Sh. Naveen Jindal, MP Kurukshetra constituency convening by Smt. A. Mona Sreenivas, Deputy Commissioner to review the progress and funds of Centrally Sponsored Development Schemes of Govt. of India. like MGNREGA,IAY, SGSY, WaterShed (Public Health), Total Sanitation Programme, Land Record Computerisation, National Rural Health Mission etc .
Superintendent of Police, ADC, Kaithal, Director, NHRM, SDMs of District Kaithal and Head of the Departments of District had attended this meeting to submit the progress reports of their Department.
NIC- Kaithal has compiled the progress of various development schemes and made necessary arrangements for presentation of review of development works and funds utilization.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


