CSI-Nihilent eGovernance Award 2010-11 Award of Excellence under District Category to Nanded

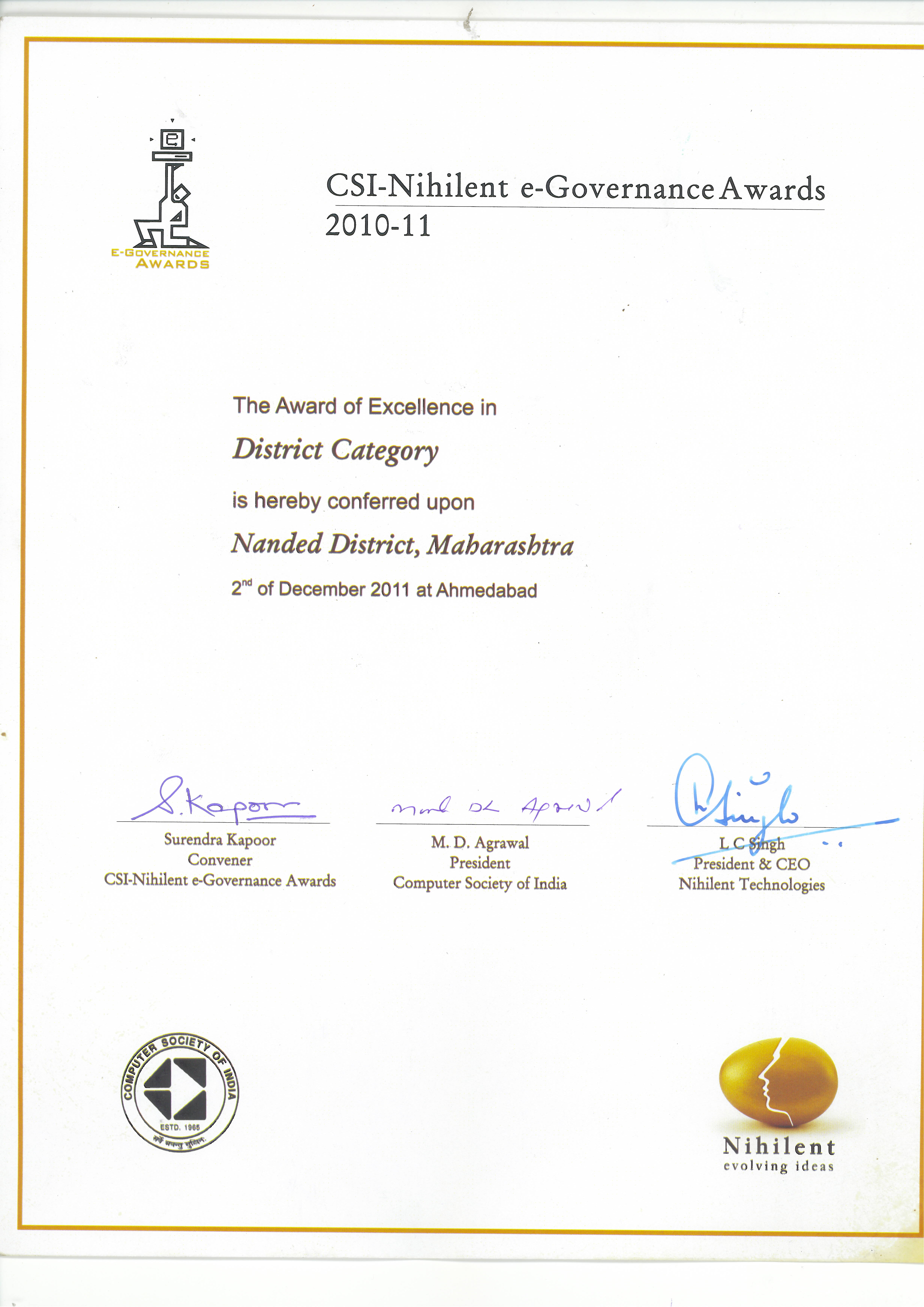
Nanded District (Maharashtra) has been selected for CSI-Nihilent eGovernance Award 2010-11, the Award of Excellence under District Category. The Award was presented to the District during the 46th Annual National Convention of Computer Society of India at Ahmedabad on 2nd December 2011. The Award was received by Dr. Shrikar Pardeshi IAS, District Collector, Dr.Nishikant Deshpande, RDC, Shri Rajesh D. Bhusari, DIO, NIC and Shri Sunil D. Potekar, DIA, NIC, Nanded. The award was presented by the eminent scientist Dr. V. Rajaraman , Shri Surendra Kapoor, Convener, Shri. M.D. Agrawal, President, CSI and Shri L.C.Singh, President and CEO, Nihilent Technology at a glittering function.
Credit goes to NIC, Dr Shrikar Paradeshi IAS DM, Nanded
NIC has developed web based application software called PARADISE for online application filing and certificate generation. This software was basic element to bring all 310 CSCs on single platform. The prepaid accounting feature of this software has proved a helping hand in accounting process. All the services are standardized and the GOM has issued a GR to implement this software at all Districts in Maharashtra. Till date 12 Districts have started the implementation. Shri Moiz Hussain, SIO, Maharashtra, has provided precious guidance to DIO and DIA NIC Nanded in development of this software. The credit of this award goes to NIC and Collectorate Team.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


