Inauguration of Web based GIS Portal of the Gajapati District, Orissa
Inauguration of Web based GIS Portal of the District:
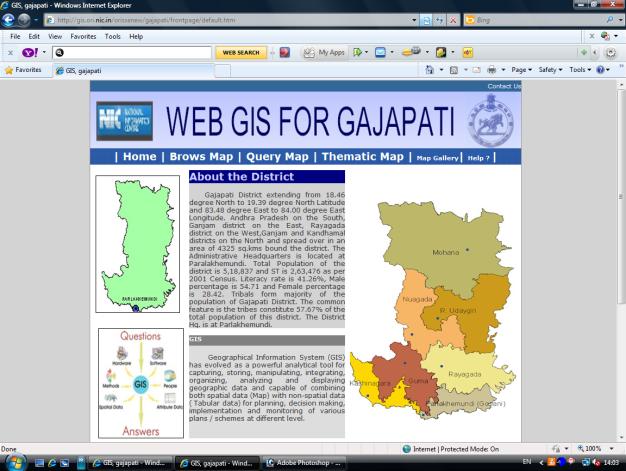
http://gis.ori.nic.in/orissanew/gajapati/frontpage/default.htm
NIC District Centre, Gajapati, moved into its new building duly inaugurated by Shri P.C.Das, District Collector on 20/04/2011.
On this occasion, the GIS portal, specifically designed for Gajapati district under guidance of Dr. Manjurani Routray, Scientist-E & Head, GIS Division, NIC Orissa State Unit, was inaugurated by District Collector. Shri Bijaya Kumar Samal, Scientist-D, GIS Div., NIC Orissa presented various features of the Web-GIS to all district heads. Role based user credentials have been provided to the district administration for updation of the database on the server.
The programme was coordinated by Shri T. Balakrishna Murty, DIO & Scientist-C & Shri R. R. Majhi, S.O/Engr-SB. The programme concluded with the vote of thanks by the DIO.
- NIC District Unit, Gajapati




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


